For over three decades, the Linux kernel has been almost exclusively written in C — a language celebrated for its speed, low-level control, and portability. But beneath that performance lies a chronic vulnerability: memory safety bugs. Buffer overflows, use-after-free errors, and data races have plagued operating system kernels since their inception, accounting for a significant portion of critical security vulnerabilities.
Now, a quiet revolution is underway. Rust, a systems programming language engineered from the ground up for memory safety, is being integrated into the Linux kernel — and it could change everything.
The Memory Safety Crisis in Systems Programming
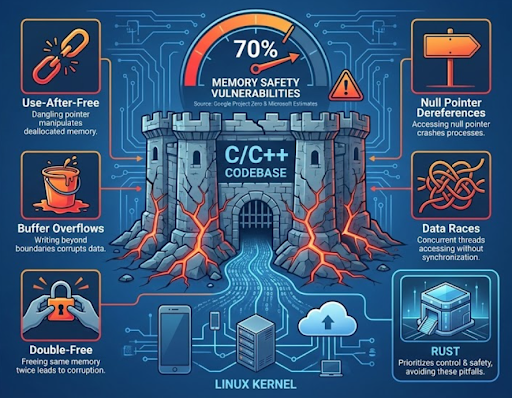
Memory safety bugs aren’t an edge case — they’re endemic to C and C++ development. Google’s Project Zero estimates that approximately 70% of serious security vulnerabilities in large C/C++ codebases are attributable to memory safety issues. Microsoft reported similar figures for its own products.
For a piece of software as critical as the Linux kernel — which runs everything from Android phones to cloud servers powering global infrastructure — this is not an acceptable baseline.
The Most Common Memory Bugs in C/C++
- Use-After-Free (UAF): Memory is freed, but a dangling pointer continues to reference it, allowing attackers to manipulate deallocated memory regions.
- Buffer Overflows: Writing beyond allocated memory boundaries can corrupt adjacent data or enable arbitrary code execution.
- Double-Free: Freeing the same memory block twice leads to heap corruption and potential code injection.
- Null Pointer Dereferences: Accessing memory through a null pointer crashes processes or allows exploitation.
- Data Races: Concurrent threads accessing shared memory without proper synchronization produce undefined, often exploitable behavior.
These issues persist not because of developer incompetence, but because C’s design philosophy prioritizes control over safety. Rust was built to provide the same level of control — without these pitfalls.
Why Rust? The Case for Memory Safety by Design
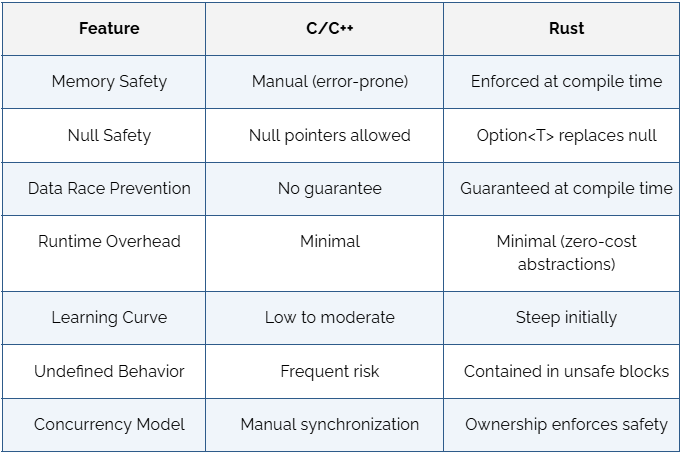
Rust’s core innovation is its ownership model — a compile-time system of rules governing how memory is accessed, transferred, and released. Unlike garbage-collected languages (which impose runtime overhead) or C/C++ (which leave safety to the developer), Rust enforces safety guarantees at compile time with zero runtime cost.
Rust’s Key Safety Guarantees
- Ownership and Borrowing: Each value has a single owner. References (borrows) are strictly controlled — you cannot have a mutable reference and an immutable reference simultaneously.
- Lifetime System: The compiler tracks how long references are valid, making use-after-free errors a compile-time failure, not a runtime crash.
- No Null Pointers: Rust uses Option<T> instead of null, forcing developers to handle the “no value” case explicitly.
- Fearless Concurrency: The type system prevents data races at compile time, a near-impossible guarantee in C or C++.
- Unsafe Blocks: Low-level operations requiring raw pointer access are isolated in explicit unsafe{} blocks, making risky code auditable and contained.
Rust Enters the Linux Kernel
The landmark moment came in December 2022 when Linus Torvalds merged Rust support into Linux 6.1 — the first time in the kernel’s 30-year history that a second programming language was officially supported. The decision followed years of community debate and was championed by Miguel Ojeda, who developed the Rust-for-Linux project and contributed the initial infrastructure.
What Has Been Implemented So Far
- Core Rust infrastructure integrated into the kernel build system (Kbuild)
- Rust abstractions for kernel primitives: spinlocks, reference counting, work queues
- Initial Rust-written device drivers, including an Apple AGX GPU driver by Asahi Linux
- A Rust-based NVMe storage driver that demonstrated competitive performance with its C equivalent
The integration is deliberately gradual. New drivers and subsystems are being written in Rust while existing C code remains in place. The kernel is not being rewritten — Rust is being adopted where it provides the clearest safety and maintainability benefits.
Industry Adoption: Beyond the Kernel
The Linux kernel is part of a much broader shift. The Rust market has seen remarkable growth across systems programming, embedded development, web infrastructure, and security-critical applications. The Stack Overflow Developer Survey has ranked Rust as the most admired programming language for nine consecutive years.
Sectors Adopting Rust at Scale
- Cloud Infrastructure: Amazon Web Services, Microsoft Azure, and Google have deployed Rust in performance-critical services.
- Operating Systems: Microsoft is rewriting core Windows components in Rust. Android has integrated Rust into its codebase since 2021.
- Embedded Systems: Rust is gaining traction in firmware development for IoT and safety-critical systems.
- Web Assembly: Rust is one of the primary languages targeting WebAssembly for high-performance browser applications.
- Cybersecurity: Security tooling and cryptography libraries are increasingly being developed in Rust due to its safety properties.
Companies like Yalantis, a software development firm known for building scalable applications, have embraced Rust for systems-level and high-performance projects, reflecting a broader industry trend of experienced development teams investing in Rust expertise to future-proof their engineering capabilities.
Challenges and Criticisms
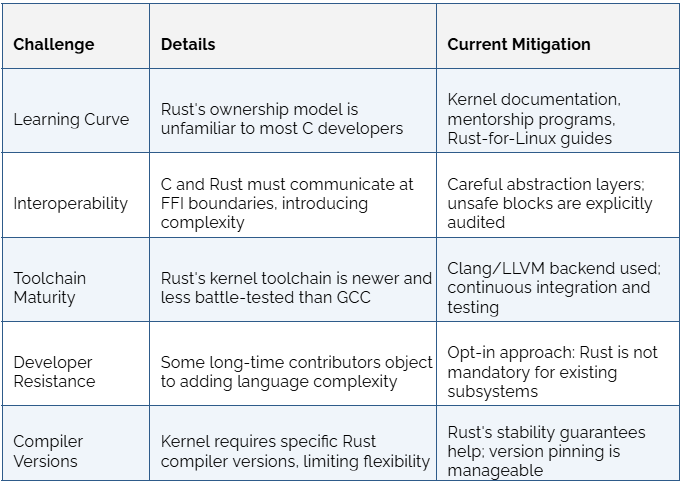
The transition is not without friction. Critics and kernel veterans have raised legitimate concerns about Rust’s integration into a decades-old, highly specialized codebase.
The Road Ahead: A Safer Kernel
The long-term vision is compelling. As Rust tooling matures and a new generation of kernel contributors grows comfortable with the language, the expectation is that safety-critical subsystems — memory management, networking, file systems — will increasingly be implemented or reimplemented in Rust.
What the Future May Look Like
- New subsystems in Rust: Drivers, file systems, and network modules written from scratch will default to Rust where feasible.
- Gradual C replacement: As Rust abstractions mature, maintainers may choose to port existing C subsystems to reduce long-term vulnerability surface.
- Policy evolution: Major tech organizations funding Linux development (Google, Microsoft, Meta) have publicly supported Rust adoption, which will likely accelerate contributions.
- Safety tooling: Formal verification tools and expanded compiler diagnostics will further reduce the already-narrow margin for unsafe code.
The Linux kernel’s adoption of Rust is not a rejection of C’s legacy — it is an acknowledgment that the threat landscape has changed. The exploits targeting memory corruption vulnerabilities are increasingly sophisticated, automated, and devastating. Rust offers a principled engineering response: eliminate entire classes of bugs by construction, not by convention.
Conclusion
The memory safety revolution is not hypothetical — it is already compiling. With Rust support merged into the mainline Linux kernel, backed by the world’s largest technology companies and a rapidly expanding developer community, the question is no longer whether Rust will reshape systems programming, but how quickly.
For an operating system that powers the majority of the world’s servers, phones, and embedded devices, the stakes could not be higher. Rust is not just a new language for the Linux kernel. It may be its most important upgrade in a generation.


